This subject continues to fascinate me to the nth degree. I have tried keeping tabs on Stuxnet…Operation Olympic Games and Cyber Warfare. I have covered some of these topics in past posts to this blog.
A little context here…
What was Operation Olympic Games
After years of downplaying offensive U.S. cyber capabilities and fretting about Chinese cyber weapons, a major assumption has been turned on its head: America has now conceded that it conducted the most sophisticated state-sponsored cyber attack in the history of civilization.
This history-making development was reported by the Times’ David Sanger in his new book Confront and Conceal: Obama’s Secret Wars and Surprising Use of American Power. We now know that the United States has spent billions, hidden in non-public budgets, to develop a capacity to attack the infrastructure of Iran.
This has gone on even as the State Department and the White House have been desperately seeking a series of treaties and agreements to regulate and reign in such activities by others. When President Obama declared, on May 29, 2009, that America’s “digital infrastructure” was a “national strategic asset” and would be protected as such, he defined what was largely seen as a defensive policy on cyber attack: We won’t do anything to you unless you do something to us.
Wikipedia says
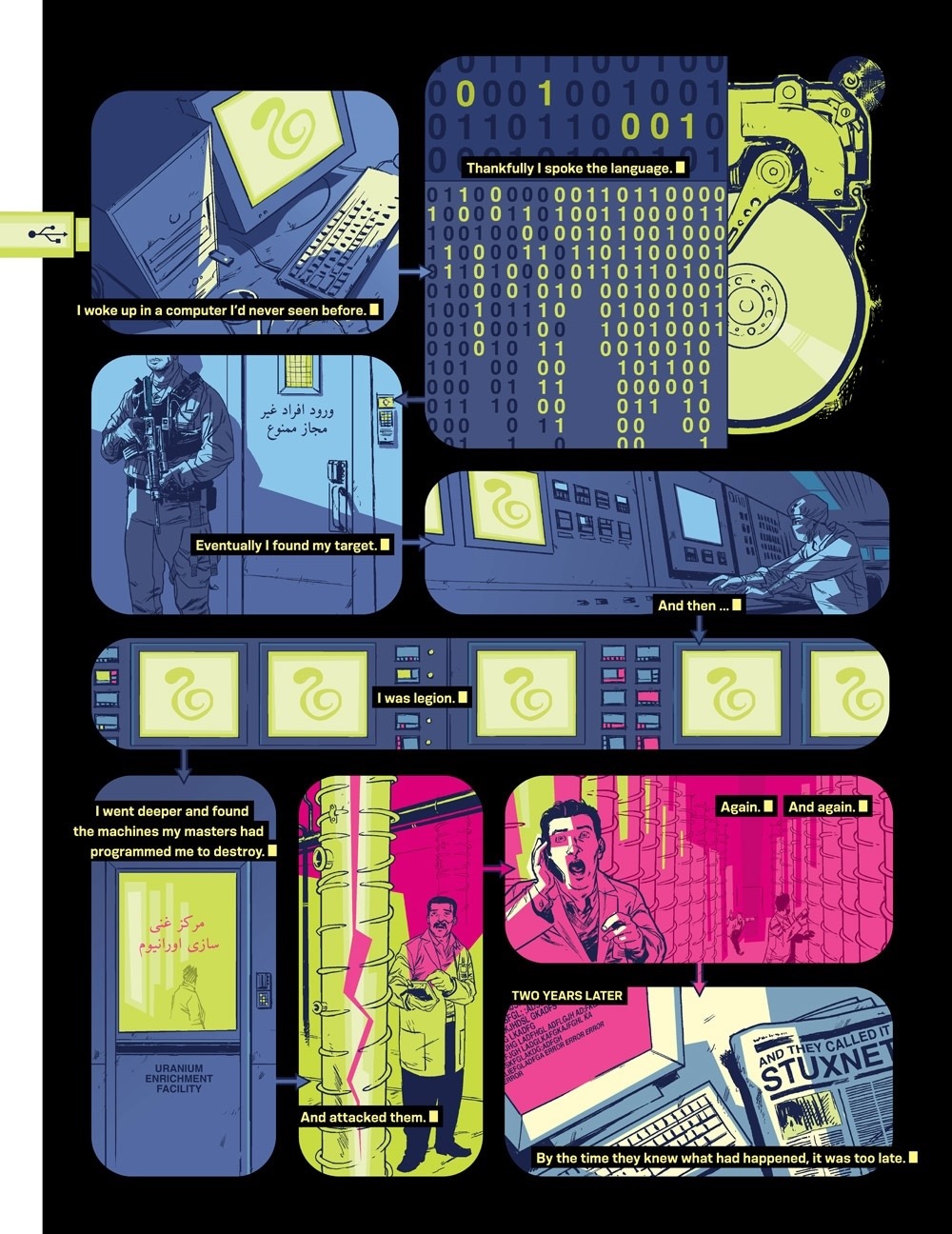
Operation Olympic Games was a covert and still unacknowledged campaign of sabotage by means of cyber disruption, directed at Iranian nuclear facilities by the United States and likely Israel. As reported, it is one of the first known uses of offensive cyber weapons.[1] Started under the George W. Bush administration in 2006, Olympic Games was accelerated under President Obama, who heeded Bush’s advice to continue cyber attacks on Iranian nuclear facility at Natanz.[1] Bush believed that the strategy was the only way to prevent an Israeli conventional strike on Iranian nuclear facilities.[1]
Contents [hide]
1 History
2 Significance
3 Leak Investigation
4 See also
5 References
6 Further reading
History[edit]During Bush’s second term, General James Cartwright along with other intelligence officials presented Bush with a sophisticated code that would act as an offensive cyber weapon. “The goal was to gain access to the Natanz plant’s industrial computer controls…the computer code would invade the specialized computers that command the centrifuges.”[1] Collaboration happened with Israel’s SIGINT intelligence service, Unit 8200. Israel’s involvement was important to the Americans because the former had “deep intelligence about operations at Natanz that would be vital to making the cyber attack a success.”[1] Additionally, American officials wanted to “dissuade the Israelis from carrying out their own preemptive strike against Iranian nuclear facilities.”[1] To prevent a conventional strike, Israel had to be deeply involved in Operation Olympic Games. The computer virus created by the two countries became known as “the bug,” and Stuxnet by the IT community once it became public. The malicious software successfully, but temporarily, halted approximately 1000 of the 5000 centrifuges from spinning at Natanz.
A programming error in “the bug” caused it to spread to computers outside of Natanz. When an engineer “left Natanz and connected [his] computer to the Internet, the American- and Israeli-made bug failed to recognize that its environment had changed.”[1] The code replicated on the Internet and was subsequently exposed for public dissemination. IT security firms Symantec and Kaspersky Lab have since examined Stuxnet. It is unclear whether the Americans or Israelis introduced the programming error.
Significance[edit]According to the Atlantic Monthly, Olympics Games is “probably the most significant covert manipulation of the electromagnetic spectrum since World War II, when cryptanalysts broke the Enigma cipher that allowed access to Nazi codes.”[2] The New Yorker claims Operation Olympic Games is “the first formal offensive act of pure cyber sabotage by the United States against another country, if you do not count electronic penetrations that have preceded conventional military attacks, such as that of Iraq’s military computers before the invasion of 2003.”[3] Therefore, “American and Israeli official action can stand as justification for others.”[3]
The Washington Post reported that Flame malware was also part of Olympic Games.[4]
Wikipedia Operation Olympic Games entry
The New York Times article that exposed Olympic Games
WASHINGTON — From his first months in office, President Obama secretly ordered increasingly sophisticated attacks on the computer systems that run Iran’s main nuclear enrichment facilities, significantly expanding America’s first sustained use of cyberweapons, according to participants in the program.
Mr. Obama decided to accelerate the attacks — begun in the Bush administration and code-named Olympic Games — even after an element of the program accidentally became public in the summer of 2010 because of a programming error that allowed it to escape Iran’s Natanz plant and sent it around the world on the Internet. Computer security experts who began studying the worm, which had been developed by the United States and Israel, gave it a name: Stuxnet.At a tense meeting in the White House Situation Room within days of the worm’s “escape,” Mr. Obama, Vice President Joseph R. Biden Jr. and the director of the Central Intelligence Agency at the time, Leon E. Panetta, considered whether America’s most ambitious attempt to slow the progress of Iran’s nuclear efforts had been fatally compromised.
“Should we shut this thing down?” Mr. Obama asked, according to members of the president’s national security team who were in the room.
Told it was unclear how much the Iranians knew about the code, and offered evidence that it was still causing havoc, Mr. Obama decided that the cyberattacks should proceed. In the following weeks, the Natanz plant was hit by a newer version of the computer worm, and then another after that. The last of that series of attacks, a few weeks after Stuxnet was detected around the world, temporarily took out nearly 1,000 of the 5,000 centrifuges Iran had spinning at the time to purify uranium.
Times article on Olympic Games
Stuxnet
Stuxnet was just a small part of a huge campaign to disable and set back Irans Nuclear ambitions by years.
I first read about it in Wired Magazine.
Natanz technicians in white lab coats, gloves and blue booties were scurrying in and out of the “clean” cascade rooms, hauling out unwieldy centrifuges one by one, each sheathed in shiny silver cylindrical casings.
Any time workers at the plant decommissioned damaged or otherwise unusable centrifuges, they were required to line them up for IAEA inspection to verify that no radioactive material was being smuggled out in the devices before they were removed. The technicians had been doing so now for more than a month.
“We were not immune to the fact that there was a bigger geopolitical picture going on. We were definitely thinking … do I really want my name to be put on this?” – Eric Chien
Normally Iran replaced up to 10 percent of its centrifuges a year, due to material defects and other issues. With about 8,700 centrifuges installed at Natanz at the time, it would have been normal to decommission about 800 over the course of the year.But when the IAEA later reviewed footage from surveillance cameras installed outside the cascade rooms to monitor Iran’s enrichment program, they were stunned as they counted the numbers. The workers had been replacing the units at an incredible rate — later estimates would indicate between 1,000 and 2,000 centrifuges were swapped out over a few months.
The question was, why?
Iran wasn’t required to disclose the reason for replacing the centrifuges and, officially, the inspectors had no right to ask. Their mandate was to monitor what happened to nuclear material at the plant, not keep track of equipment failures. But it was clear that something had damaged the centrifuges.
What the inspectors didn’t know was that the answer they were seeking was hidden all around them, buried in the disk space and memory of Natanz’s computers. Months earlier, in June 2009, someone had silently unleashed a sophisticated and destructive digital worm that had been slithering its way through computers in Iran with just one aim — to sabotage the country’s uranium enrichment program and prevent President Mahmoud Ahmadinejad from building a nuclear weapon.
Another Wired article suggests
As Iran met in Kazakhstan this week with members of the UN Security Council to discuss its nuclear program, researchers announced that a new variant of the sophisticated cyberweapon known as Stuxnet had been found, which predates other known versions of the malicious code that were reportedly unleashed by the U.S. and Israel several years ago in an attempt to sabotage Iran’s nuclear program.
The new variant was designed for a different kind of attack against centrifuges used in Iran’s uranium enrichment program than later versions that were released, according to Symantec, the U.S-based computer security firm that reverse-engineered Stuxnet in 2010 and also found the latest variant.
The new variant appears to have been released in 2007, two years earlier than other variants of the code were released, indicating that Stuxnet was active much earlier than previously known. A command-and-control server used with the malware was registered even earlier than this, on Nov. 3, 2005.
Like three later versions of Stuxnet that were released in the wild in 2009 and 2010, this one was designed to attack Siemens PLCs used in Iran’s uranium enrichment program in Natanz.
But instead of changing the speed of spinning centrifuges controlled by the PLCs, as those later versions did, this one focused on sabotaging the operation of valves controlling the flow of uranium hexafluoride gas into the centrifuges and cascades — the structure that connects multiple centrifuges together so that the gas can pass between them during the enrichment process. The malware’s goal was to manipulate the movement of gas in such a way that pressure inside the centrifuges and cascade increased five times the normal operating pressure.
“That would have very dire consequences in a facility,” says Liam O’Murchu, manager of security response operations for Symantec. “Because if pressure goes up, there’s a good chance the gas will turn into a solid state, and that will cause all sorts of damage and imbalances to the centrifuges.”
Cyber war it is on
Since Stuxnet there have been several more attacks. I would venture to bet there are some taking place now that are undetected.
Symantec PDF on Stuxnet
Overview
In 2010, Symantec reported on a new and highly sophisticated worm called Stuxnet. This worm became known as the first computer software threat that was used as a cyber-weapon. The worm was specifically designed to take control over industrial plant machinery and making them operate outside of their safe or normal performance envelope, causing damage in the process. This was a first in the history of malware.
Clues in the code pointed to other versions of the worm which could potentially perform different actions leaving an open question about Stuxnet and how it came to be. The wait for the missing link is now over. Symantec have now discovered an older version of Stuxnet that can answer the questions about the evolution of Stuxnet. This newly discovered variant has been dissected and analyzed in detail and here is a summary of our key findings:
• Stuxnet 0.5 is the oldest known Stuxnet version to be analyzed, in the wild as early as November 2007 and in development as early as November 2005.
• Stuxnet 0.5 was less aggressive than Stuxnet versions 1.x and only spread through infected Step 7 projects.
• Stuxnet 0.5 contains an alternative attack strategy, closing valves within the uranium enrichment facility at Natanz, Iran, which would have caused serious damage to the centrifuges and uranium enrichment system as a whole.
Flame for example
“Kaspersky Lab announces the discovery of a highly sophisticated malicious program that is actively being used as a cyber weapon attacking entities in several countries. The complexity and functionality of the newly discovered malicious program exceed those of all other cyber menaces known to date.
“The malware was discovered by Kaspersky Lab’s experts during an investigation prompted by the International Telecommunication Union (ITU). The malicious program, detected as Worm.Win32.Flame by Kaspersky Lab’s security products, is designed to carry out cyber espionage. It can steal valuable information, including but not limited to computer display contents, information about targeted systems, stored files, contact data and even audio conversations.
“The independent research was initiated by ITU and Kaspersky Lab after a series of incidents with another, still unknown, destructive malware program – codenamed Wiper – which deleted data on a number of computers in the Western Asia region. This particular malware is yet to be discovered, but during the analysis of these incidents, Kaspersky Lab’s experts, in coordination with ITU, came across a new type of malware, now known as Flame. Preliminary findings indicate that this malware has been “in the wild” for more than two years – since March 2010. Due to its extreme complexity, plus the targeted nature of the attacks, no security software detected it.
“Although the features of Flame differ compared with those of previous notable cyber weapons such as Duqu and Stuxnet, the geography of attacks, use of specific software vulnerabilities, and the fact that only selected computers are being targeted all indicate that Flame belongs to the same category of super-cyberweapons….”
(((More.)))
http://hackmageddon.com/2012/05/28/a-flame-on-the-cyberwarfare-horizon/
(…)
“The Malware is a sophisticated attack toolkit, It is a backdoor, a Trojan, and has worm-like features (three in one). According to Kaspersky its development has taken a couple of years and it will probably take year to fully understand the 20MB of code of Flame.
“According to CrySyS Lab Flame has been in the wild since 2007, having been seen in the following geographical regions: Europe on Dec 5 2007, The United Arab Emirates on Apr 28 2008 and the Islamic Republic of Iran on Mar 1 2010;
“Flame is controlled via an SSL channel by a C&C infrastructure spread all around the world, ranging from 50 (Kaspersky) to 80 (CrySyS) different domains;
New Stuxnet information
Fascinating new article about Stuxnet in Foreign Policy today. It turns out Stuxnet may have been more complex and far different than first reported. It attacked in multiple ways… Using a vast trove of zero day exploits amongst other things.
Three years after it was discovered, Stuxnet, the first publicly disclosed cyberweapon, continues to baffle military strategists, computer security experts, political decision-makers, and the general public. A comfortable narrative has formed around the weapon: how it attacked the Iranian nuclear facility at Natanz, how it was designed to be undiscoverable, how it escaped from Natanz against its creators’ wishes. Major elements of that story are either incorrect or incomplete.
That’s because Stuxnet is not really one weapon, but two. The vast majority of the attention has been paid to Stuxnet’s smaller and simpler attack routine — the one that changes the speeds of the rotors in a centrifuge, which is used to enrich uranium. But the second and “forgotten” routine is about an order of magnitude more complex and stealthy. It qualifies as a nightmare for those who understand industrial control system security. And strangely, this more sophisticated attack came first. The simpler, more familiar routine followed only years later — and was discovered in comparatively short order.With Iran’s nuclear program back at the center of world debate, it’s helpful to understand with more clarity the attempts to digitally sabotage that program. Stuxnet’s actual impact on the Iranian nuclear program is unclear, if only for the fact that no information is available on how many controllers were actually infected. Nevertheless, forensic analysis can tell us what the attackers intended to achieve, and how. I’ve spent the last three years conducting that analysis — not just of the computer code, but of the physical characteristics of the plant environment that was attacked and of the process that this nuclear plant operates. What I’ve found is that the full picture, which includes the first and lesser-known Stuxnet variant, invites a re-evaluation of the attack. It turns out that it was far more dangerous than the cyberweapon that is now lodged in the public’s imagination.
More tidbits
This new Stuxnet variant was almost entirely different from the old one. For one thing, it was much simpler and much less stealthy than its predecessor. It also attacked a completely different component of the Natanz facility: the centrifuge drive system that controls rotor speeds.
This new Stuxnet spread differently too. The malware’s earlier version had to be physically installed on a victim machine, most likely a portable engineering system, or it had to be passed on a USB drive carrying an infected configuration file for Siemens controllers. In other words, it needed to be disseminated deliberately by an agent of the attackers.
The new version self-replicated, spreading within trusted networks and via USB drive to all sorts of computers, not just to those that had the Siemens configuration software for controllers installed. This suggests that the attackers had lost the capability to transport the malware to its destination by directly infecting the systems of authorized personnel, or that the centrifuge drive system was installed and configured by other parties to which direct access was not possible.
What’s more, Stuxnet suddenly became equipped with an array of previously undiscovered weaknesses in Microsoft Windows software — so-called “zero day” flaws that can fetch hundreds of thousands of dollars on the open market. The new Stuxnet also came equipped with stolen digital certificates, which allowed the malicious software to pose as legitimate driver software and thus not be rejected by newer versions of the Windows operating system.
All this indicates that a new organization began shaping Stuxnet — one with a stash of valuable zero days and stolen certificates. In contrast, the development of the overpressure attack can be viewed as the work of an in-group of top-notch industrial control system security experts and coders who lived in an exotic ecosystem quite remote from standard IT security. The overspeed attacks point to the circle widening and acquiring a new center of gravity. If Stuxnet is American-built — and, according to published reports, it most certainly is — then there is only one logical location for this center of gravity: Fort Meade, Maryland, the home of the National Security Agency.
We have entered a new age of warfare… The Gloves are off. I thought this next insight was very interesting and in many ways very true. Any why this is so fascinating and historically significant.
Looking at the two major versions of Stuxnet in context leaves a final clue — a suggestion that during the operation, something big was going on behind the scenes. Operation Olympic Games — the multiyear online espionage and sabotage campaign against the Iranian nuclear program — obviously involved much more than developing and deploying a piece of malware, however sophisticated that malware was. It was a campaign rather than an attack, and it appears that the priorities of that campaign shifted significantly during its execution.
When my colleagues and I first analyzed both attacks in 2010, we first assumed that they were executed simultaneously, maybe with the idea to disable the cascade protection system during the rotor-speed attack. That turned out to be wrong; no coordination between the two attacks can be found in the code. Then we assumed that the attack against the centrifuge drive system was the simple and basic predecessor after which the big one was launched, the attack against the cascade protection system. The cascade protection system attack is a display of absolute cyberpower. It appeared logical to assume a development from simple to complex. Several years later, it turned out that the opposite was the case. Why would the attackers go back to basics?
The dramatic differences between both versions point to changing priorities that most likely were accompanied by a change in stakeholders. Technical analysis shows that the risk of discovery no longer was the attackers’ primary concern when starting to experiment with new ways to mess up operations at Natanz. The shift of attention may have been fueled by a simple insight: Nuclear proliferators come and go, but cyberwarfare is here to stay. Operation Olympic Games started as an experiment with an unpredictable outcome. Along the road, one result became clear: Digital weapons work. And different from their analog counterparts, they don’t put military forces in harm’s way, they produce less collateral damage, they can be deployed stealthily, and they are dirt cheap. The contents of this Pandora’s box have implications much beyond Iran; they have made analog warfare look low-tech, brutal, and so 20th century.
In other words, blowing the cover of this online sabotage campaign came with benefits. Uncovering Stuxnet was the end of the operation, but not necessarily the end of its utility. Unlike traditional Pentagon hardware, one cannot display USB drives at a military parade. The Stuxnet revelation showed the world what cyberweapons could do in the hands of a superpower. It also saved America from embarrassment. If another country — maybe even an adversary — had been first in demonstrating proficiency in the digital domain, it would have been nothing short of another Sputnik moment in U.S. history. So there were plenty of good reasons not to sacrifice mission success for fear of detection.
Foreign Policy article on Stuxnet
Highlighting one more thing
Much has been written about the failure of Stuxnet to destroy a substantial number of centrifuges or to significantly reduce Iran’s enriched-uranium production. While that is undisputable, it doesn’t appear that either was the attackers’ intention. If catastrophic damage had been caused by Stuxnet, that would have been by accident rather than on purpose. The attackers were in a position where they could have broken the victim’s neck, but they chose continuous periodical choking instead. Stuxnet is a low-yield weapon with the overall intention of reducing the lifetime of Iran’s centrifuges and making the Iranians’ fancy control systems appear beyond their understanding.
Reasons for such tactics are not difficult to identify. When Stuxnet was first deployed, Iran had already mastered the production of IR-1 centrifuges at industrial scale. During the summer of 2010, when the Stuxnet attack was in full swing, Iran operated about 4,000 centrifuges, but kept another 5,000 in stock, ready to be commissioned. A one-time destruction of the Iranians’ operational equipment would not have jeopardized that strategy, just like the catastrophic destruction of 4,000 centrifuges by an earthquake back in 1981 did not stop Pakistan on its way to getting the bomb. By my estimates, Stuxnet set back the Iranian nuclear program by two years; a simultaneous catastrophic destruction of all operating centrifuges wouldn’t have caused nearly as big a delay.
Centrifuge inventory at Natanz between 2008 and 2010. Iran constantly kept a stockpile of at least 50 percent spare centrifuges, invalidating the idea that a simultaneous catastrophic destruction of all operating centrifuges would have meant the end of its nuclear ambitions.
The low-yield approach also offered added value. It drove Iranian engineers crazy, up to the point where they might have ultimately ended up in total frustration about their capabilities to get a stolen plant design from the 1970s running and to get value from their overkill digital protection system. When comparing the Pakistani and Iranian uranium-enrichment programs, one cannot fail to notice a major performance difference. Pakistan basically managed to go from zero to successful low-enriched uranium production within just two years during shaky economic times, without the latest in digital control technology. The same effort took Iran over 10 years, despite the jump-start from Pakistan’s A.Q. Khan network and abundant money from sales of crude oil. If Iran’s engineers didn’t look incompetent before, they certainly did during the time when Stuxnet was infiltrating their systems.
Legend has it that in the summer of 2010, while inflicting its damage on Natanz, Stuxnet “escaped” from the nuclear facility due to a software bug that came with a version update. While that is a good story, it cannot be true. Stuxnet propagated only between computers that were attached to the same local network or that exchanged files though USB drives. In other words, Stuxnet must have spread largely by human hands. But in these days of remote access by modem or via Internet virtual private networks, human hands can extend across continents.
Contractors serving at Natanz worked for other clients as well. And those contractors most likely carried their Stuxnet-infected laptop computers to their secondary clients and connected their laptops to the clients’ “local” networks. Let’s say they spread it to a cement plant. That cement plant then had other contractors, who in turn connected their mobile computers to the infected “local” network. Those computers carried the malware farther — to another cement plant, maybe in another country. At some link in the chain, infected contractors or employees remotely accessed their machines, allowing the virus to travel over continents. All of a sudden, Stuxnet has made its way around the globe — not because of the fact that billions of systems are connected to the Internet, but because of the trusted network connections that tunnel through the Internet these days. For example, remote maintenance access often includes the capability to access shared folders online, giving Stuxnet a chance to traverse through a secure digital tunnel. My colleagues and I saw exactly that when we helped Stuxnet-infected clients in industries completely unrelated to the nuclear field back in 2010.
Given that Stuxnet reported Internet protocol addresses and hostnames of infected systems back to its command-and-control servers, it appears that the attackers were clearly anticipating (and accepting) a spread to noncombatant systems and were quite eager to monitor that spread closely. This monitoring would eventually deliver information on contractors working at Natanz, their other clients, and maybe even clandestine nuclear facilities in Iran.
A Sputnik moment. Years from now it will be looked at as such.
Flame further reading:
Click to access w32_duqu_the_precursor_to_the_next_stuxnet.pdf
skywiper aka Flame
Flame questions and answers
https://www.securelist.com/en/blog/208193522/The_Flame_Questions_and_Answers

Heya i’m for the primary time here. I came across this board
and I to find It truly helpful & it helped me out much.
I am hoping to present one thing again and help others like you aided me.
LikeLike
Hello to every body, it’s my first pay a quick visit of this blog; this webpage carries remarkable and in fact fine material in support of
visitors.
LikeLike
the method is quite excellent. But I dona??t consider everybody can put into action it.
3ds xl r4 http://3ds-xl-r4.menabwn.com
LikeLike
Hello it’s me, I am also visiting this website regularly, this site is
actually good and the viewers are actually sharing nice thoughts.
LikeLike
I used to be suggested this website by way of my cousin.
I am not certain whether this put up is written by him
as nobody else recognize such precise about my difficulty. You are amazing!
Thank you!
LikeLike
Hello Dear, are you in fact visiting this website regularly, if so afterward you will without doubt obtain fastidious experience.
LikeLike
Under the Merge options section be sure to select Form Letters for the “Document type” and
E-mail for “Merge to. You may also want to pay attention to the setting to confirm email deletion, in case you think you might accidentally remove a message if there’s no prompt asking if you’re sure you want to delete something. For instance, I could create an email that could look like one from Toyota Motor Corporation to one of its world-wide vendors and elicit them to give out information that ought not to have been shared.
LikeLike
hi!,I like your writing so a lot! percentage wee keep up a corresponddnce
moree appproximately your article on AOL? I require an expert on thus space to solvee my problem.
May be that is you! Having a look forward to look you.
LikeLike
Hey There. I found your weblog using msn. That is a very neatly written article.
I will be sure to bookmark it and come back to learn extra of your helpful information. Thank you for the post.
I will definitely comeback.
LikeLike
Hi! I simply want to offer you a huge thumbs up for your great info you
have here on this post. I’ll be returning to your blog for
more soon.
LikeLike
I got this website from my pal who told me regarding this web site and at the moment this time I am visiting this website and reading very informative articles at this
place.
LikeLike
Excellent pieces. Keep posting such kind of information on your blog.
Im really impressed by it.
Hi there, You have performed an incredible job. I will definitely digg it and
personally suggest to my friends. I’m sure they will be
benefited from this site.
LikeLike
Excellent way of describing, and nice paragraph to take information regarding my presentation focus, which i am going to deliver in academy.
LikeLike
Howdy this is kinda of off topic but I was wondering if blogs use WYSIWYG editors or if
you have to manually code with HTML. I’m starting a blog soon but
have no coding skills so I wanted to get guidance from someone with experience.
Any help would be greatly appreciated!
LikeLike
Stuxnet was a sub-part of the larger “Olympic Games” operation. By comparison, a small part, unbelievably enough.
LikeLike